Cyber Attacks on Activists Traced to FinFisher Spyware of Gamma
Cyber Attacks on Activists Traced to FinFisher Spyware of Gamma
By Vernon Silver – 25 July, 2012 – Bloomberg
It’s one of the world’s best-known and elusive cyber weapons: FinFisher, a spyware sold by U.K.- based Gamma Group, which can secretly take remote control of a computer, copying files, intercepting Skype calls and logging every keystroke.
For the past year, human rights advocates and virus hunters have scrutinized FinFisher, seeking to uncover potential abuses. They got a glimpse of its reach when a FinFisher sales pitch to Egyptian state security was uncovered after that country’s February 2011 revolution. In December, anti-secrecy website WikiLeaks published Gamma promotional videos showing how police could plant FinFisher on a target’s computer.
Enlarge image Cyber Attacks on Activists Traced to FinFisher
Husain Abdulla, a U.S. citizen who is director of Americans for Democracy and Human Rights in Bahrain, is considering lawsuits and a complaint to the U.S. State Department about the border-crossing hack. Source: Husain Abdulla via Bloomberg
Enlarge image Citizen Lab Security Researcher Morgan Marquis-Boire
Morgan Marquis-Boire, a security researcher at Citizen Lab, analyzed the infected e-mails for this story. Photographer: Jacob Kepler/Bloomberg
Enlarge image Bill Marzcak
Marczak found evidence that traces malicious software e-mailed to Bahraini activists back to FinFisher, a spyware sold by U.K.-based Gamma Group. Photographer: David Paul Morris/Bloomberg
“We know it exists, but we’ve never seen it — you can imagine a rare diamond,” says Mikko Hypponen, chief research officer at Helsinki-based data security company F-Secure Oyj. (FSC1V) He posted the Egypt documents online last year and said if a copy of the software itself were found, he’d write anti-virus protection against it.
Now he may get his wish.
Researchers believe they’ve identified copies of FinFisher, based on an examination of malicious software e-mailed to Bahraini activists, they say. Their research, which is being published today by the University of Toronto Munk School of Global Affairs’ Citizen Lab, is based on five different e-mails obtained by Bloomberg News from people targeted by the malware.
Global Reach
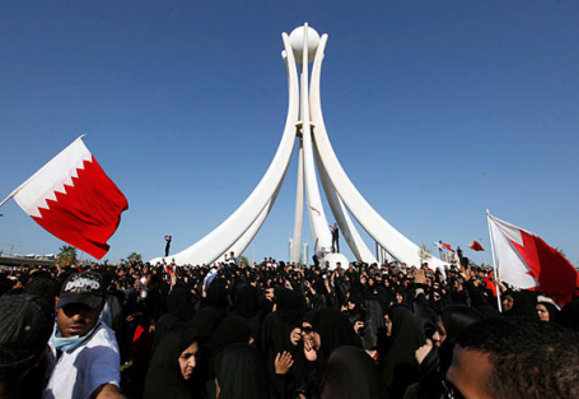
Pro-democracy activists received the malware in Washington, London and Manama, the capital of Bahrain, the Persian Gulf kingdom that has been gripped by tension since a crackdown on protests last year.
The findings illustrate how the largely unregulated trade in offensive hacking tools is transforming surveillance, making it more intrusive as it reaches across borders and peers into peoples’ digital devices. From anywhere on the globe, the software can penetrate the most private spaces, turning on computer web cameras and reading documents as they are being typed.
“Selling software that allows for the taking over of computers without rule of law can lead to abuse,” says Courtney Radsch, senior program manager for freedom of expression at Washington-based Freedom House, which promotes human rights. …more























Add facebook comments
Kick things off by filling out the form below.
Leave a Comment